Advisory for the mitigation of the WPA2 protocol attacks
update 1: 16/10/2017 18:00 CET
In response to the recently disclosed WPA2 Key Reinstallation AttaCKS KRACKS , Steelcyber Scientific issues the following advisory to help system and network administrators/IT professionals and users to understand and mitigate the vulnerability. The attack technique does not concern the core and client in-house client infrastructure of Steelcyber Scientific (we use wired connections), however the pervasiveness of WiFi and the number of devices concerning this vulnerability merit special attention.
What is it: It is a protocol implementation bug that affects both WiFi end devices (Android and Apple smartphones, Windows/Linux/Apple desktops/laptops that use a WiFi connection) as well as Wifi routers. A current list of all affected devices/vendors can be accessed here. All major Wifi device vendors are affected by this.
What can the attacker do: Due to a bug in the WPA2 connection handshake protocol implementation, an attacker can trick the WiFi client to install an invalid key and thus allowing the attacker to decrypt/have access to all traffic to/from the targeted WiFi device. To achieve this, there needs to be a duplicate/rogue SSID within the range of the victim's WiFi client device that operates with the same credentials (SSID, MAC address), usually operating on a different WiFi channel than the original access point. This allows the attacker to execute a 'man in the middle' attack and at best, the attacker is able to watch all packets to/from the victim's device. Depending on whether the destination website is configured to use only HTTPS enabled traffic (some sites can operate in port 80 mode), the attacker can also strip/force a non encrypted session on the victim and thus login credentials can be obtained. In addition, depending on various configuration options of the WPA2 enabled WiFi router, the attacker might also be able to hijack TCP connections and inject malware online to the victim's device.
Is this actively being exploited? : Steelcyber Scientific does not at present have knowledge of an ongoing exploit of this vulnerability, beyond the (non publicly available) demo tools the authors demonstrated.
How can network administrators mitigate this vulnerability: In the absence of available vendor patches (at the time of writing) that should be your first priority , the following recommendations can help mitigate the threat
- Do NOT turn WPA2 off in favour of weaker options (WEP). Having a weaker by design and obsolete protocol instead of a vulnerable one does not protect you but makes things worse.
- Limit the transmission power-range of repeaters/routers and disable 802.11r (fast roaming functionality) where possible.
- Where possible enable/use the AES-CCMP encryption protocol instead of the WPA-TKIP or GCMP ones. While this will not stop the man in the middle attack, it can seriously hinder the attacker in the process of TCP connection hijacking.
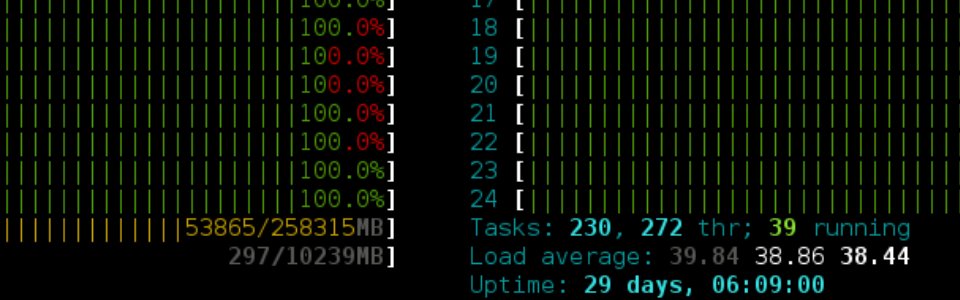
- Proactively, have a professional monitor/dedicated computer with a WiFi card to monitor SSID and channels. The first stage of this attack is to duplicate your SSID with a rogue one and sending carefully crafted packets to the WiFi devices victims to trick them to connect there. The rogue SSID is likely to operate on a different channel, so if you have setups that operate on specific channels and these change, chances are that you are under attack.
- If WiFi connected users report suddenly websites that use to have a green lock (https traffic) and suddenly they switch to non encrypted traffic (http), do investigate.